 Wire fraud is one of the most financially damaging threats to people and businesses today. Victims can lose hundreds of thousands of dollars in the blink of an eye.
Wire fraud is one of the most financially damaging threats to people and businesses today. Victims can lose hundreds of thousands of dollars in the blink of an eye.
What is wire fraud? Let’s start with the basics:
A wire transfer is an electronic transfer of funds between entities, usually a bank and someone else.
Wire fraud is the use of this system to steal money.
Typically this is done by fooling a financial institution into wiring money to a fraudulent account. The process often begins with the theft of personal data or email credentials, which means data security is paramount to preventing this threat.
Below we provide an overview of wire fraud so you better protect your business and clients.
Three out of four attempts of any type of fraud involves a wire transfer, according to a report from Guardian Analytics.
This is not surprising given the size of the target. The amount of money transferred across telecommunications reached $600 trillion in 2012. When there is that much money in play, scammers will always look to take advantage.
Wire-fraud attacks have increased ten-fold since 2003, according to the Wall Street Journal, and they continue to evolve to better take advantage of security flaws.
Related - Ransomware: How to prevent a crypto crisis at your business
Wire transfer fraud is a complex problem. Scammers can gather information and launch attacks in a dizzying number of ways.
Most attacks begin with the theft of a victim’s email credentials or enough personal data to impersonate the victim at a financial institution. The attacker then tricks the bank into wiring money to a fraudulent account and *poof* the money is gone.
This graphic from the Guardian report shows a few ways this can happen. As you can see, attackers have a long list of tactics to choose from.
Attackers use methods such as malware, phishing, and social engineering to get information or email credentials. They then have an equally broad number of ways to approach the financial institution, as described in the report:
The number of ways that scammers can attack financial institutions and victimize individuals and businesses is not limited to these types, either. Scammers continue to innovate and develop new ways to take advantage of security flaws.
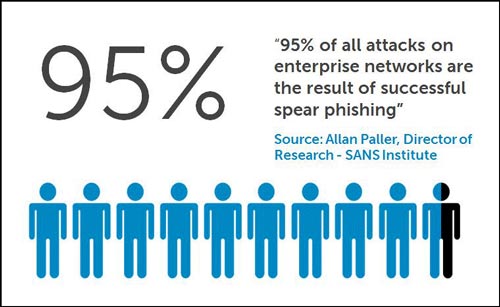
Spear phishing is a common tactic attackers will use to initiate a wire fraud scheme.
Traditional phishing involves sending an enormous number of emails in hopes of catching a few fish. This approach has grown less effective in recent years, with growing awareness of what the emails look like, so attackers have moved on to a more targeted approach.
Spear phishing involves sending fewer, higher-quality emails to a narrower target. The emails appear to be from a trustworthy source by including personal information or other data acquired by the attacker.
Spear phishing emails are very effective. Their targeted nature gives them a boost in credibility with remarkably better results for attackers.
The emails attempt to lower the individual’s guard and often include a malicious link that, when clicked, compromises the individual’s machine. It can also attempt to get the person to reply with personal information.
Once an attacker receives enough information, he then uses it to attempt wire transfer fraud.
Related - Ransomware: How to prevent a crypto crisis at your business
The AccesEnforcer UTM firewall from Calyptix has many features that can help to protect against wire fraud:
Wire fraud is a serious problem that requires a multi-faceted approach. With enough training of personnel, deployment of security solutions, and steady vigilance, businesses and financial institutions can cut risk and avoid becoming victims.
Related resources
Internet Crime and Scams from FBI Annual Report
Top 7 Network Attack Types in 2015 So Far
DDoS Attacks: Trends show a stronger threat in 2015
Ransomware Prevention: 5 ways to avoid a crisis