 Healthcare does not parallel other industries in many respects – especially in cyber security.
Healthcare does not parallel other industries in many respects – especially in cyber security.
The top causes of data breaches in healthcare are different than those of other industries, according to a new report from Verizon.
The 2018 Protected Health Information Data Breach Report suggests healthcare is unique in that most of its data breaches are caused by internal actors rather than external ones.
For example, human error and privilege misuse caused far more security incidents reviewed in the report than hacking and malware.
The difference with other industries may be exaggerated by the stringent reporting requirements imposed by HIPAA – but healthcare also has a long list of cyber security problems.
Do you have the right priorities when working in healthcare cyber security? See the five top data breach causes below to find out.
About the Data
The report’s data is based on 1,368 security incidents gathered from 2015 to 2017. All of the incidents meet the following criteria:
Almost all of the incidents (94%) are also considered data breaches by the report’s authors. Nearly three quarters are from the U.S. with the rest coming from 26 other countries.
One-third of security incidents in the report were not intentionally caused – i.e. were errors.
This should not be surprising. Healthcare offices are often the nexus of regulation, bureaucracy, technology, and science – all existing in multiple layers. Mistakes are to be expected.
The most common types of errors are shown in the table below.
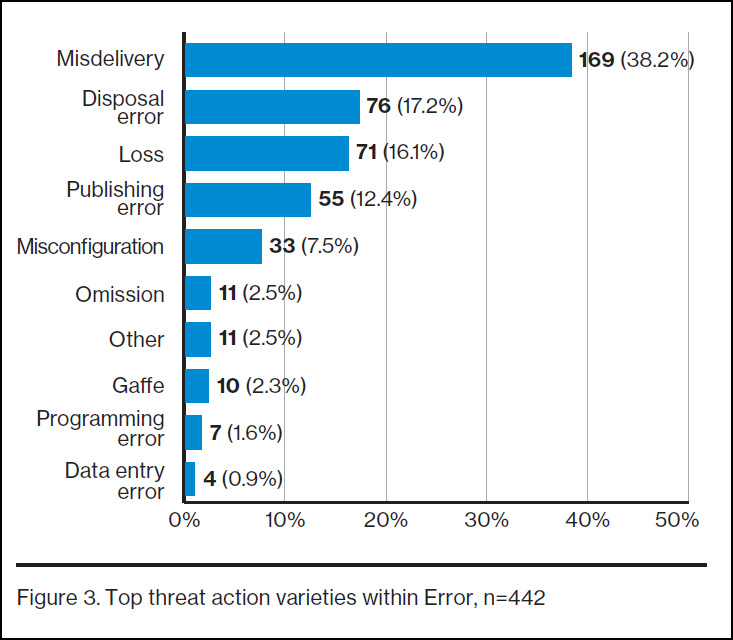
Three types of errors account for more than 70% of the total in this category:
Misdelivery (38.2%) – example: sending sensitive medical information to the wrong patient.
Disposal error (17.2%) – example: discarding medical documents without shredding them.
Loss (16.1%) – example: misplacing a thumb drive that contains unprotected medical records.
Paper Documents Are Breached, Too
With the constant stream of news stories about data breaches involving electronic medical records, it’s easy to forget the staggering volume of paper records most organizations use to store protected health information (PHI).
Looking to the types of assets most commonly exposed in error-related security incidents, documents top the list, as shown in the table below.
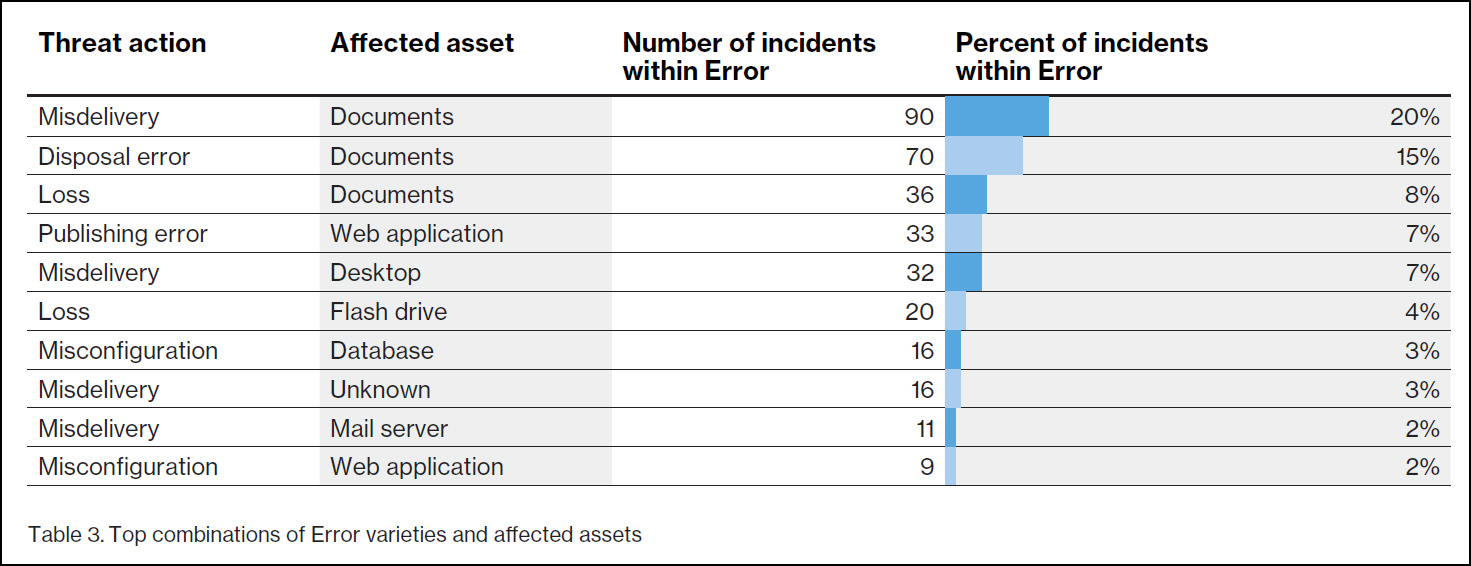
Totaling the top three items shows at least 43% of assets compromised in error-related security incidents affected hard-copy documents, not electronic records.
Almost another one-third of healthcare security incidents involved a person abusing their use of internal resources.
For example, a lab technician may be granted access to a database for purposes of data entry and later misuse that access to snoop on patients, resulting in a data breach.
This is an example of “privilege abuse” which is associated with two-thirds of security incidents in this category, as you can see in the table below.
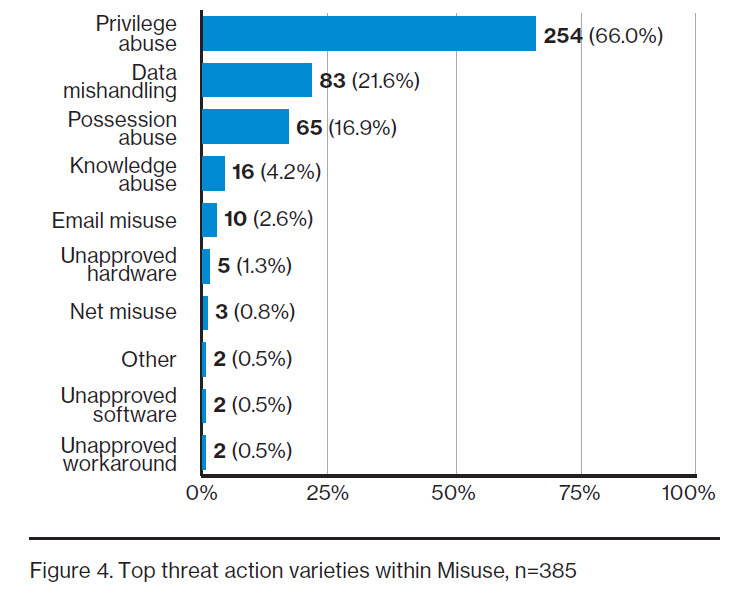
“Possession abuse” is similar to “privilege abuse” but is associated with a physical asset – such as a paper document. Combining these categories reveals 82.9% of error-related incidents are caused by people misusing authorized access to sensitive data.
Ninety-five percent of security incidents with a “physical” cause were attributed to theft in the report.
Other types include snooping, tampering, and surveillance – but are far less common.
What do thieves target? Laptops, as shown in the table below.
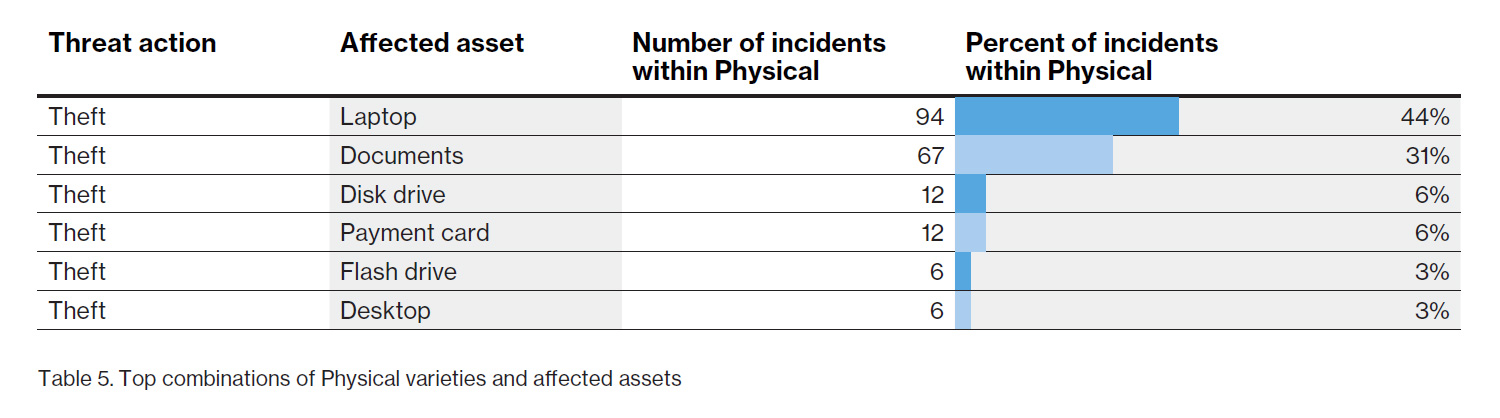
Laptops and documents account for at least 75% of all theft-related security incidents in the report.
Digging further into the data, the report also notes about half of stolen laptops (47%) are taken from cars.
When a laptop storing PHI is stolen from a hospital, is it always a HIPAA data breach? No, not if the data is encrypted.
Hacking incidents occur when a person intentionally gains unauthorized access to a system or device.
Hackers have many techniques, but one of their favorites is to steal access credentials. That’s usually easier than cracking a system manually.
To put it another way, when a thief wants to break into a safe, it’s often easier to steal the keys rather than crack the lock.
The power of credentials is why hackers target them so often, as you can see in the table below.
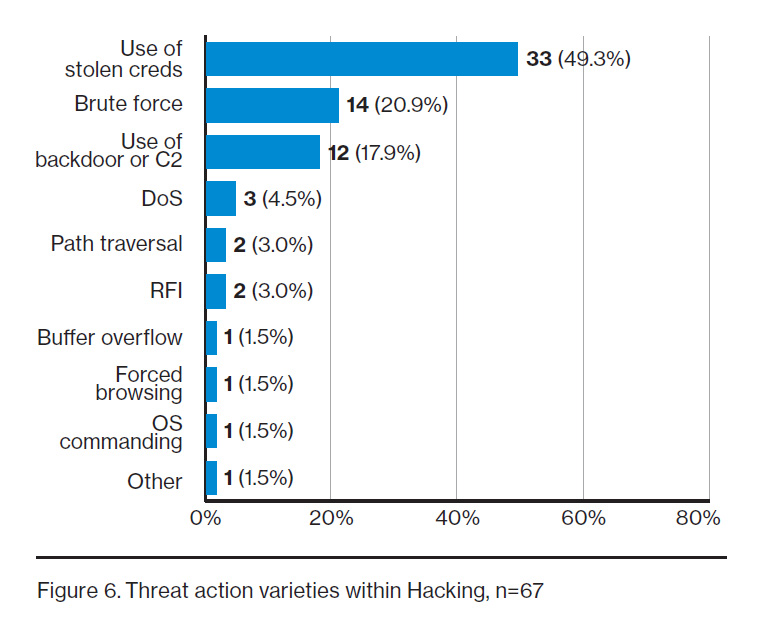
Nearly half of incidents attributed to hacking involve the use of stolen credentials. An additional one-in-five are brute-force attacks (i.e. systematically attempting to guess the credentials).
Combining these two, that’s slightly more than 70% of hacking incidents related to authentication credentials.
Malicious software is one of the top causes of data breaches around the world, and today much of it is ransomware. This is true across industries, including healthcare.
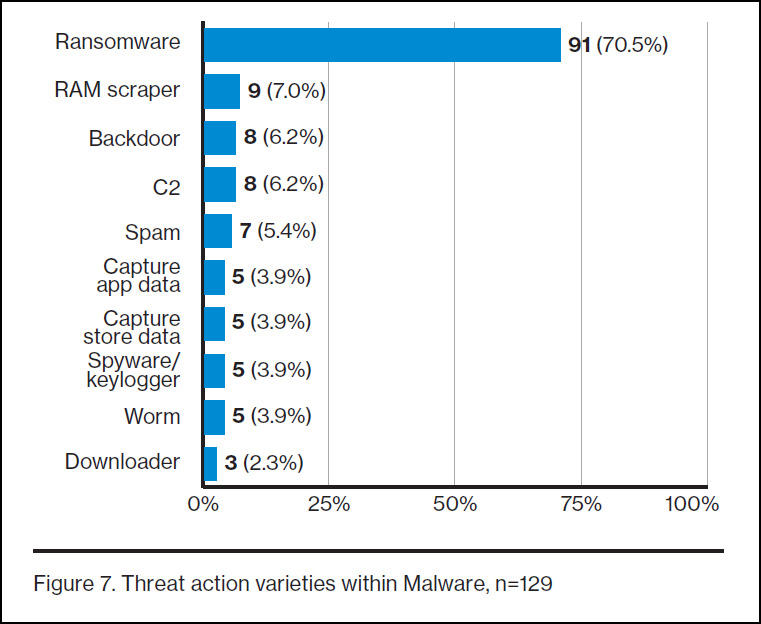
70.5% of all security incidents involving malware were attributed to ransomware in the report.
This is not surprising since malware authors are often financially motivated. Ransomware offers a simple business model to turn malicious code into cash.
Digging further into the report shows the top healthcare assets attacked by ransomware are databases, servers, and desktops in that order (excluding “unknown” assets).
Is a ransomware attack a HIPAA breach? Not always.
The second most common type of attack in this category – RAM scrapers – are associated with only 7% of all malware-related incidents, most of them on healthcare POS systems.
Insiders are a Bigger Problem in Healthcare
Healthcare is the only industry in which staff members (i.e. “internal actors”) are behind more data breaches than hackers or other outside threats (i.e. “external actors”), according to the report.
This is further proof of the unique challenges healthcare faces in cyber security when compared to other industries.
Looking only at data breaches (in this report, it includes security incidents when PHI was either at risk or confirmed as disclosed), about 58% were caused by internal actors and 42% were caused external ones.
Why Staff Members Breach
While a hacker or a smash-and-grab thief is almost always motivated by money, internal actors have a wider range of motives, as shown in the table below.
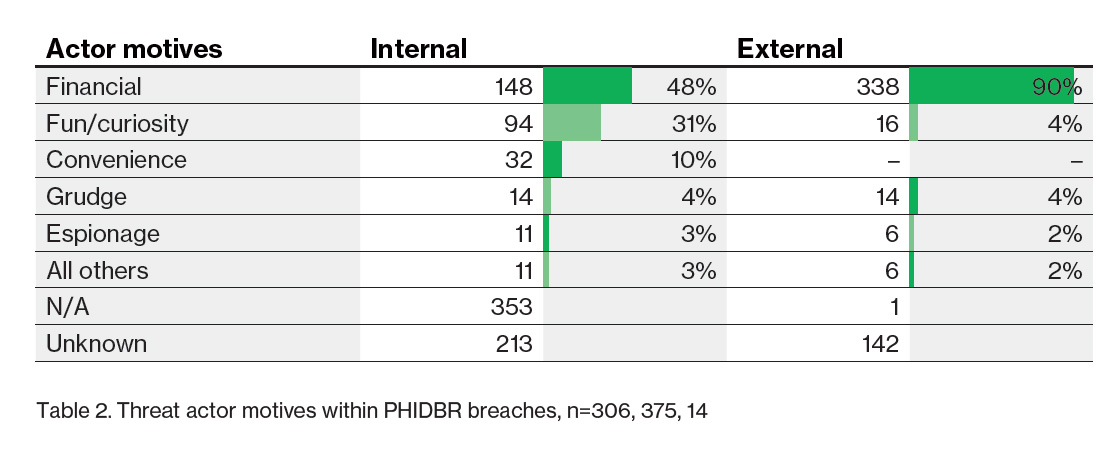
Most healthcare data breaches that involve an internal actor are caused (at least in part) by human error, according to the report. The table above does not list “human error”, but the report’s authors note it is captured by the “N/A” category.
Setting aside “N/A” and “unknown”, about half of insiders (48%) were financially motivated and nearly one-third (31%) were motivated by fun or curiosity – such as when a staff member peaks into the medical records of an acquaintance or celebrity.
Verizon 2018 Protected Health Information Data Breach Report
Discover the top 3 causes of HIPAA violations and their simple solutions
Hospital Ransomware Attacks: A HIPAA Breach?