Hackers can attack your business in dozens of ways. A key to understanding how they may attack is to first ask, why?
The top motives of hackers, in descending order:
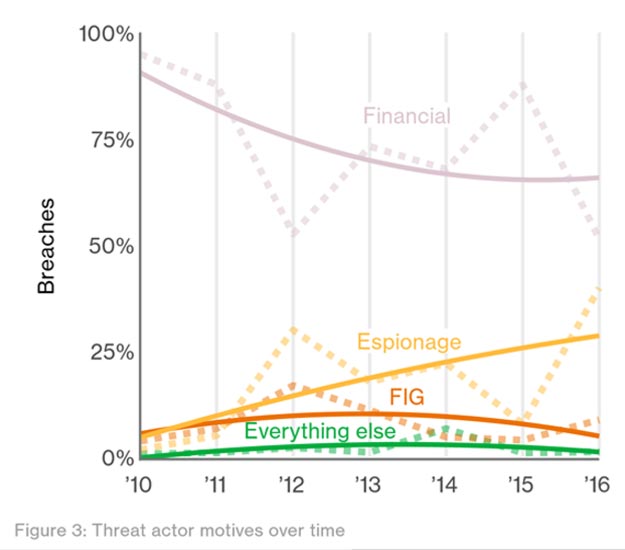
The results are based on the data breaches analyzed in the 2017 Verizon Data Breach Investigations Report.
A massive 93% of breaches studied were motivated by financial gain or espionage. The remaining 7% is split between FIG and everything else.
 Motive #1. Financial Gain
Motive #1. Financial GainFinancial gain is what motivates hackers most often. This was true in 2016, spurring attacks such as one that hit Bangladesh Bank last February.
Hackers were able to nab $80 million from the bank by compromising account credentials for the bank’s international transaction account.
Attacks in Every Industry
Financial institutions aren’t the only ones being peppered with these types of attacks either – industries such as Accommodation and Food Services, Healthcare, Information, and Retail have all been targeted by hackers for financial information, according to the Verizon DBIR.
Hackers, like anyone motivated by money, want the most amount of return they can get for the amount of effort they put in.
Targeting small businesses or industries that have lax security rules can result in a successful attack without much work for the hacker.
In fact, it can be more lucrative for a hacker to target multiple Mom and Pop shops than to target a larger company such as Bank of America, given the difference in security measures for these two types of companies.
Tactics in Financial Attacks
Tactics such as social engineering have made it easy for hackers to gain access to sensitive information with one simple well-crafted email or spoofed site. Attacks such as these can easily fool an untrained employee into forking over information.
Other tactics hackers primarily employed when siphoning financial data included using stolen credentials, installing a backdoor/c2 malware, using spyware/keylogging programs, and exporting sensitive information to private storage.
Common avenues for financially motivated hacks include web applications, email attachments, email, and backdoor/c2 malware.
 Motive #2. Espionage
Motive #2. EspionageHackers motivated by espionage tend to focus on one or two types of information: political or manufacturing.
Hackers can and have leveraged corporate and government secrets for gain.
Stealing Trade Secrets
In manufacturing espionage, hackers look for secrets they or their employers can use for a competitive edge.
ThyssenKrupp was the unlucky target of such an attack at the end of 2016.
The German steel company discovered trade secrets regarding their steel production and manufacturing plant design divisions had been compromised by hackers from southeast Asia.
The company has since said that the damage of these attacks was ‘impossible to estimate’ given the nature of the breach.
Election Hacking
For other hackers, the insight into another country’s political, military or intelligence secrets is more than enough motivation to launch an espionage attack.
The DNC hack that occurred this past year immediately comes to mind when discussing this type of attack.
Attackers wormed their way to sensitive information by disseminating several rounds of phishing emails to employees at the DNC. Data stolen in the attack was used to influence the 2016 U.S. Presidential Election.
9 out of 10 Are State-Affiliated
While 10% of espionage attacks were orchestrated by nation-state affiliates, competitors, and former employees, a whopping 90% were initiated by state-affiliated groups.
Hackers largely targeted public administration and manufacturing, with an increasing focus on educational institutions.
The preferred method for gathering highly sensitive information was phishing.
 Motive #3. FIG (Fun, Ideology, and Grudge)
Motive #3. FIG (Fun, Ideology, and Grudge)The FIG category consists of several less common, but just as serious motivations behind data breaches.
In all three subsections of this category, common tactics for attacks included privilege abuse, data mishandling, possession abuse, and stolen credentials.
Hackers used web applications, LAN access, remote access and physical access to carry put these types of attacks.
Fun
Breaches initiated for fun, such as a hospital employee looking at a celebrity’s health records, fall into this category
While usually not intended to be malicious, breaches conducted for fun are still breaches, leaving the company on the hook for thousands, possibly millions, in fines, all for someone’s idea of a good time.
Ideology
Ideological attacks typically develop from a disagreement over politics or values between the target and the attacker.
Hacktivism, Cyber Terrorism, and Cyber Vandalism all stem from differences in ideology between the victim and assailant.
Grudge
Grudge attacks can be carried out by a disgruntled employee or loved one who is seeking revenge after they feel they have been wronged.
Using credentials that still work after termination and selling secrets to competitors are both avenues attackers can use to exact their revenge.
This category encompasses all other miscellaneous motivations for data breaches. Things such as employee error and system malfunctions fall into this group.
Similar to the Fun category, some of these breaches are not meant to be malicious. But even so, a breach is a breach, and the ramifications of one regardless of intention can be severe.
Verizon 2017 Data Breach Investigations Report
Practice These 10 Basic Cyber Hygiene Tips for Risk Mitigation
5 Easy Ways Small IT Departments can Train Employees on Network Security