 Malware continues to evolve, finding new ways to penetrate systems, establish persistence – and of course avoid detection.
Malware continues to evolve, finding new ways to penetrate systems, establish persistence – and of course avoid detection.
Fileless malware avoids detection by minimizing its footprint on the disk of the infected system.
Instead of storing code in a dedicated file on the hard drive, a fileless attack stores malicious code in memory, i.e. RAM, without writing it to disk.
This bypasses traditional, file-based approaches to malware detection. Also, when the system restarts, the RAM is cleared and the malicious code disappears.
Fileless malware is not new, but it’s growing in volume and sophistication – so let’s brush up on the topic.
“Fileless malware” is a bit of a misnomer. It would be more accurately described as “mostly fileless”.
The infection typically begins with a static file – usually an attachment downloaded from a phishing email.
Files can also spread through malvertising, malicious downloads, and other common means – but phishing emails are the most common vector.
The attachment has a seemingly benign file type – such as a Microsoft Word document – that can execute macros.
Once a victim downloads and opens the file, if it’s a malicious Word document, then by default the user must click “OK” to “enable content”. This enables the embedded macro to run.
The macro executes a series of commands opening a hidden instance of a powerful utility, usually Windows PowerShell.
PowerShell is a command-line shell and scripting language created to help administrators automate system and application management. Like many powerful tools, it’s a mighty weapon in the wrong hands.
Administrators can set “restricted” policies to limit PowerShell execution, but these can be easily overridden by attackers, according to research from McAfee.
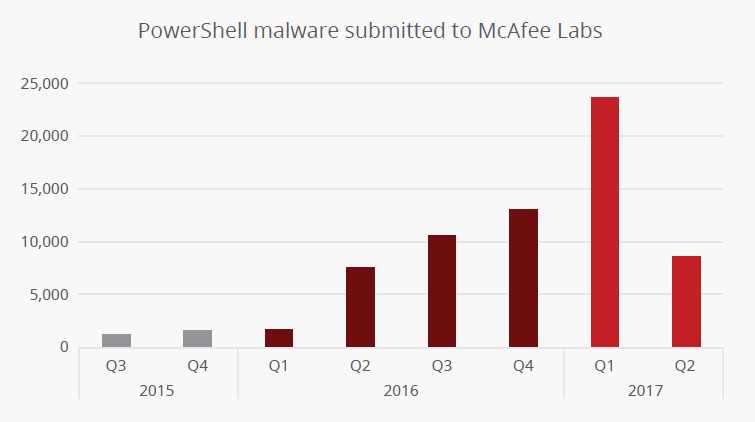
Malware infections that leverage PowerShell are not new, but they are growing more common, according to McAfee.
Once the infection gains access to PowerShell, it connects to a remote server to download a payload (i.e. more commands and code).
For example, the instance of PowerShell on the victim’s machine can gather system information and send it to the attacker’s remote command-and-control (C2C) server.
The C2C server can then reply with commands tailored to the environment.
Here’s where the infection goes “fileless”.
Rather than storing the downloaded payload in a file on the disk of the infected machine, the instance of PowerShell is instructed to hide it.
One place is in RAM. PowerShell can store the data in a hive in the Windows registry and store the hive in memory rather than the file system.
Malicious code can also be injected into running processes such as svchost.exe, using their memory space.
The malicious code is not stored in dedicated files. Instead, it’s embedded into existing resources and is executed using common utilities.

Now attackers can step toward their goal. They can establish a backdoor in the system, install additional malware, perform click-fraud, or complete many other nasty tasks.
PowerShell commands can also delete the static file – the original Word document – that started the infection. This makes detection and analysis more difficult.
Also, when a machine is restarted, any malicious code stored in RAM is erased, further complicating efforts to uncover the attack.
Malware rarely conforms to a single type or category. Variants often combine multiple tactics and means of infection, which can complicate discussions.
Here are some malware variants that hide their code in memory.
Restaurants Hit with Fileless Malware
A sophisticated fileless attack was discovered in June 2017 targeting restaurants in the U.S.
Malicious Word documents – with names such as “menu.rtf” and “Olive Garden.rtf” – were attached to phishing emails to initiate infection.
Most security solutions could not detect the attack when first discovered. It granted control of an infected system, installed backdoors, and enabled the theft of financial data, according to Morphisec.
 Fileless Strain Communicates via DNS
Fileless Strain Communicates via DNS
Fileless malware discovered in March 2017 followed an infection chain similar to that described earlier in this blog post.
Malicious Word documents arrived via phishing emails. When opened and enabled, code executed that led to a PowerShell session downloading additional code and commands, hiding them in Windows Registry or Alternate Data Stream (ADS), and ultimately installing a trojan on the infected system.
What set the attack apart was its use of DNS TXT queries and responses for C2C communication between the infected machine and the attacker’s system.
“DNS traffic within corporate networks should also be considered a channel that an attacker can use to implement a fully functional, bidirectional C2 infrastructure,” according to Talos.
KOVTER Click Fraud Attack
The KOVTER trojan family has evolved steadily through the years, with recent iterations focused on secretly turning infected machines into click-fraud bots.
Infection typically begins with the receipt of a phishing email with a Microsoft Office attachment. Once opened and enabled, the malware installs several files and registry entries.
KOVTER infection continues with PowerShell injection and a technique known as “shell spawning”, according to Trend Micro.
In Oct. 2017, researchers discovered a malvertising attack used to distribute KOVTER, proving fileless malware also spreads through vectors other than email.
 Preventing Fileless Attacks
Preventing Fileless AttacksMalware continues to grow stronger and more complex – but the overwhelming majority of variants require help from the user to gain access to the system.
The best approach to fighting fileless malware is a multi-layered approach with emphasis on preventing the initial infection. Below are a few tips – but please do not consider them a complete solution.
Enact “least privilege” – Grant users access to features and systems only when necessary. Provide the minimum amount of access needed to perform their roles and no more. Consider a broad range of resources, including network assets, public websites, and and local applications.
Patch - Always apply patches and updates, prioritizing patches for critical systems and vulnerabilities. This applies to all systems – everything from a work station’s web browser to a server’s operating system. Automate patching where possible.
Filter email – Most malware infections begin with email, and fileless malware is no different. Use an effective email filter to prevent spam and malicious messages from reaching users. If possible, use an email quarantine for safe review of questionable messages.
Train users – Keep staff sharp and vigilant when checking email and browsing the web. Regularly train employees and test them – especially on email security.
Restrict PowerShell – Enable logging of PowerShell sessions and set policies to control its use. Learn more about secure PowerShell configurations.
Application Whitelisting – Control the applications available to users through app whitelisting. Block user access to PowerShell, cmd.exe, and other utilities if not needed.
Filter outbound traffic – Limit the systems accessible from your network – especially networks that contain critical assets such as credit card and customer data. Egress filtering can restrict connections to a given list of IP addresses.
McAfee Labs Threat Report – Sept 2017 (pdf)
Security 101: The Rise of Fileless Threats that Abuse PowerShell