Network attacks are launched every hour of every day, and they evolve at an astounding pace. Every year brings new attacks and trends.
Below are the top eight network attacks by type, recorded from April to June 2017, and published in the Sept. 2017 Quarterly Threat Report from McAfee Labs.
The report is based on data collected from millions of sensors managed by McAfee.
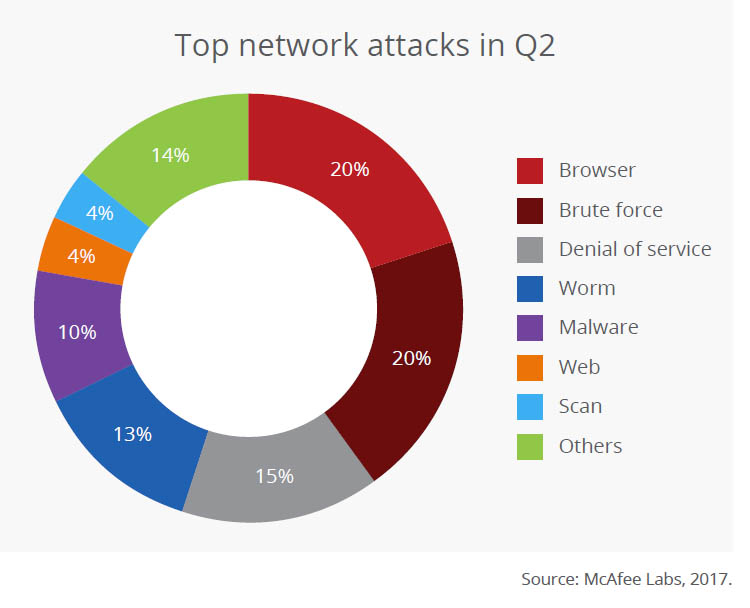
 #1. Browser Attacks – 20%
#1. Browser Attacks – 20%Browser-based network attacks tied for the second-most common type. They attempt to breach a machine through a web browser, one of the most common ways people use the internet.
Browser attacks often start at legitimate, but vulnerable, websites. Attackers breach the site and infect it with malware.
When new visitors arrive (via web browser), the infected site attempts to force malware onto their systems by exploiting vulnerabilities in their browsers.
The web browsers with the most vulnerabilities discovered in 2016 are, in descending order, according to the Symantec Internet Security Threat Report 2017:
 #2. Brute Force Attacks – 20%
#2. Brute Force Attacks – 20%Brute force attacks are akin to kicking down the front door of a network. Rather than attempting to trick a user into downloading malware, the attacker tries to discover the password for a system or service through trial and error.
These network attacks can be time consuming, so attackers typically use software to automate the task of typing hundreds of passwords.
Brute force attacks are one reason it’s important to follow password best practices, especially on critical resources such as network routers and servers.
Passwords that are long and complex are exponentially more difficult to crack via brute force than stupid passwords like “123456”, “qwerty”, and “password”. Rest assured: these are among the first keys an attacker will try.
 #3. Denial-of-Service (DDoS) Attacks – 15%
#3. Denial-of-Service (DDoS) Attacks – 15%Denial-of-service attacks, also known as distributed denial-of-service attacks (DDoS), are third on the list on the list of network security attacks, and they continue to grow stronger every year.
DDoS attacks attempt to overwhelm a resource – such as websites, game servers, or DNS servers – with floods of traffic. Typically the goal is to slow or crash the system.
One in three businesses (33%) experienced a DDoS attack in 2017, according to a Kaspersky Labs survey of 5,200 people from businesses in 29 countries. Half of respondents said DDoS attacks are growing in frequency and complexity.
DDoS can also be used to distract from other network attacks that can be far more damaging.
“In the first half of 2017, over half of those respondents affected by a DDoS attack (53%) claimed that it was used as a smokescreen,” according to Kaspersky’s press release.
 #4. Worm Attacks – 13%
#4. Worm Attacks – 13%Malware typically requires user interaction to start infection. For example, the person may have to download a malicious email attachment, visit an infected website, or plug an infected thumb drive into a machine.
Worm attacks spread on their own. They are self-propagating malware that does not require user interaction. Typically, they exploit system vulnerabilities to spread across local networks and beyond.
WannaCry ransomware, which infected more than 300,000 computers in a few days, used worm techniques to attack networks and machines.
WannaCry targeted a widespread Windows vulnerability to quickly breach a machine. Once a machine was infected, the malware scanned the connected LANs and WANs to find and infect other vulnerable hosts.
 #5. Malware Attacks – 10%
#5. Malware Attacks – 10%Malware is, of course, malicious software – applications that have been created to harm, hijack, or spy on the infect system.
It’s not clear why “worm attacks” were not included in this category – as they are typically associated with malware. Perhaps it was to emphasize the prevalence of work attacks during Q2 2017.
Regardless, malware is widespread and well known. Three common ways it spreads include:
 #6. Web Attacks – 4%
#6. Web Attacks – 4%Public-facing services – such as web applications and databases – are also targeted for network security attacks.
The most common web application attacks in Q2 2017, according to Positive Research:
 #7. Scan Attacks – 4%
#7. Scan Attacks – 4%Rather than outright network attacks, scans are pre-attack reconnaissance. Attackers use widely available scanning tools to probe public-facing systems to better understand the services, systems, and security in place.
We can only speculate on the network attack types bundled into “other”. That said, here are some of the usual suspects:
Top 7 Network Attack Types in 2016
Top 7 Network Attack Types in 2015
5 Security Controls that Stop 85% of Cyber Attacks
5 Network Security Best Practices from High-Attack Industries