 Cyber security is a challenge everywhere, but the nature of the challenge often varies by industry – including the top cause of data breaches.
Cyber security is a challenge everywhere, but the nature of the challenge often varies by industry – including the top cause of data breaches.
That’s a central theme of the 2018 Verizon Data Breach Investigations Report published last week.
The new report suggests that breach trends are best reviewed by industry rather than in aggregate – so we did that for you.
We read the 68-page breach report, pulled highlights from specific industries, and listed them below. Scroll down to see the leading causes of data breaches in your vertical.
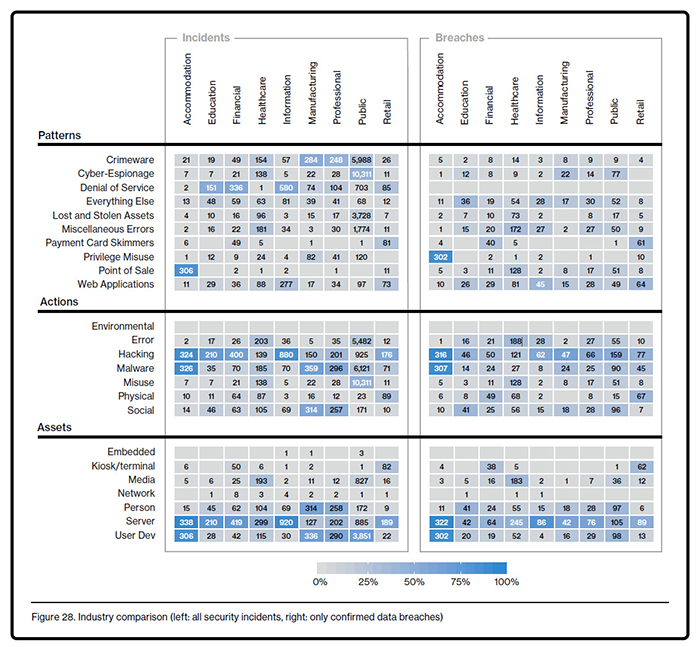
Much of the data highlighted below is based on this table, found on page 26 of the Verizon data breach report.
We found an error in the data shown above for this industry. See our post about errors found in the Verizon DBIR 2018
POS Intrusions: 89% of Breaches
Nearly 9 out of every 10 data breaches recorded in hotels in restaurants affected a point-of-sale system.
This does not include payment skimmers. Instead, POS intrusions are specifically remote attacks against payment systems within environments where card-present transactions occur.
Note: the table above lists only 5 data breaches in the POS category for this industry. This is likely a mistake. The correct number is probably 302, which is shown in the cell above.
External Attackers: 99% of Breaches
Attackers in this category are almost always based outside the organization and financially motivated. Many are linked to organized crime.
Payment Data: 93% of Breaches
Attackers who are financially motivated and who target POS systems are (of course) interested in payment data. 93% of the breaches in this category compromised information such as credit card and debit card numbers.
Hacking: 93% of Breaches
Hacking was the most common threat action reported as one of the causes of data breach. Within the hacking category, 81% of the attacks used stolen credentials.
Credentials were often taken in bulk from a POS service provider, then used to breach the POS systems of their customers, according to the Verizon DBIR.
Malware: 90% of Breaches
Malware was seen nearly as often as hacking in the data breaches in accommodation and food services.
Within malware, 96% of the identified varieties were RAM scrapers – malware designed to capture payment card data when it’s in a POS system’s memory and not encrypted.
 Education
EducationHacking: 44% of Breaches
Hacking is involved in more than 70% of the security incidents in this education. The report attributes much of this to DoS attacks, which are included in the hacking category.
Only 44% of the confirmed data breaches involved hacking.
Nearly half of the hacking-related breaches involved stolen credentials, a backdoor, or command-and-control.
Social: 41% of Breaches
Many data breaches in education involved social tactics – such as deception, manipulation, and intimidation – to exploit a person. Across all industries, 98% of social attacks are phishing or pretexting, and 96% of social attacks involve email, according to the report.
Financial Motive: 70% of Breaches
While the report fails to note whether this stat applies to security incidents or data breaches, we will go out on a limb and assume the latter.
Most attackers in education steal personal information in hopes of profiting. However, a sizeable 20% are motivated by espionage, and 14% of the breaches affected data classified as “secrets”.
 Financial and Insurance
Financial and InsuranceBanking Trojan Botnets: 27,000% of Breaches
This threat is so prevalent that the authors chose to exclude it from the report’s data to prevent it from eclipsing other insights.
Here’s how they described it:
They are “botnets that target organizations’ customers, infecting their personally owned devices with malware that captures login details. Those credentials are then used to access banking applications and other sites with authentication.”
Nearly 40,000 successful data breaches in financial and insurance companies are attributed to this threat. That’s more than 27,000% greater than the remaining 146 confirmed data breaches in this vertical.
So it’s a big problem.
Denial of Service: 56% of Incidents
Setting aside the trojan botnets, DoS attacks caused the majority of remaining security incidents recorded in financial and insurance.
However, not a single DoS was part of a successful data breach. This is true across all industries covered in the report – financial and otherwise.
 Healthcare
HealthcareWe found a mistake in the report's Healthcare section. See this error and others we found in the 2018 Data Breach Report
Internal Actors: 56% of Breaches
Healthcare is the only vertical in which internal actors caused most of the data breaches.
Only 43% were caused by external actors. Partners caused 4% and multiple parties 2%.
Errors: 35% of Breaches
Errors (i.e. mistakes) caused more data breaches in healthcare than any other type of action. Examples of errors include misdelivery, misconfiguration, and disposal errors.
Healthcare also had more than three-times more data breaches attributed to errors than any other vertical.
However, as with the public sector, this comparison is likely skewed by Verizon’s sources for data breach information and also the stringent reporting requirements of industry regulations.
The information vertical includes companies in publishing, data processing, sound recording, telecommunications, and other areas.
DoS Attacks: 56% of Incidents
While none are attributed to a breach, DoS attacks plague this vertical, accounting for more than half of the security incidents recorded. The DBIR’s authors suggest this is due to the large web presence of many of the firms.
Web Application Attacks: 41% of Breaches
Perhaps the large web presence of many of the companies in this vertical is also to blame for the prevalence of web application attacks. 45 data breaches were recorded to have this breach pattern, more than any other type.
Errors: 25% of Breaches
About one-quarter of the data breaches in the information vertical were caused by errors, often misconfigured databases and publishing errors, according to Verizon’s report.
 Manufacturing
ManufacturingState-Affiliated Attackers: 53% of Breaches
The strength of a country rests on the strength of its economy, and many nation-states want to give their companies an edge. State-sponsored attackers caused more than half of the data breaches in manufacturing.
The most common types of data stolen are personal (32%), secrets (30%), and credentials (24%).
Cyber-Espionage: 31% of Breaches
When state-sponsored hackers arrive, it’s safe to assume cyber-espionage will follow. Espionage was the leading attack pattern for breaches in manufacturing.
This trend is again reaffirmed when looking at the “actor motive”. While slightly more than half of breaches had a financial motive, 47% were motivated by espionage.
Professional, Technical, and Scientific Services
This vertical includes law offices, architects, and a variety of other business and consumer-oriented services.
Hacking: 50% of Breaches
Reviewing the attack patterns for this vertical provided little insight – but a look at the attack actions reveals that half of breaches discovered are attributed to hacking.
VERIS defines hacking as an attempt to intentionally access or harm information assets without authorization by defeating security mechanisms. Attack types include brute force and SQL injection.
Server: 58% of Breaches
At least one server was compromised in more than half of the data breaches in professional services.
Keep this in mind as Windows Server 2008 nears end-of-life, (set for Jan 14, 2020) after which Microsoft will no longer patch newly discovered vulnerabilities in the popular operating system.
 Public Administration
Public AdministrationThe number of security incidents recorded in this group – 22,788 – is more than 20-times greater than any other vertical.
As with the healthcare vertical, this may be partly due to the data sources for Verizon’s report, and is also likely influenced by the strict reporting requirements of industry regulations.
The number of data breaches in the group is 304, which is much more comparable to the other industries covered.
External Attackers: 67% of Breaches
While it’s not surprising that two-thirds of data breaches in the public sector are caused by external foes, looking deeper reveals that most of the attackers are associated with over governments.
Nearly two-thirds (63%) of the external actors are state-affiliated or nation-states (this does not include all breaches, only those for which an actor could be identified).
Also, 25% of the breaches in the public vertical are attributed to the cyber-espionage attack pattern.
Other prominent patterns – such as web application attacks, POS attacks, miscellaneous errors, and everything else – each account for about 16-17% of the breaches recorded.
Web Application Attacks: 38% of Breaches
Ecommerce systems are public-facing and typically handle payment card and customer data – making them attractive targets for cybercrime.
Roughly one-third of all confirmed breaches in retail involved a web application. Common attack types include OS commanding, SQL injection, and the use of stolen credentials to compromise the system.
Slightly more than half (53%) of the breaches recorded in retail affected a server, which may be related to the frequency of web application attacks.
Payment Card Skimming: 36% of Breaches
Another one-third of the breaches follow a pattern that is specific to brick-and-mortar retailers: card skimming. Typically, this is when an attacker sticks a device onto a card reader to secretly collect payment info as cards are swiped.
Most skimmers were discovered on gas station pumps (87%).
The strong showing in this pattern is also likely why about one-third of the assets compromised in retail data breaches were kiosks or terminals.
Errors Found in the Verizon Data Breach Report 2018
Email Phishing for IT Providers
Top 4 Insights from Verizon Data Breach Report 2017