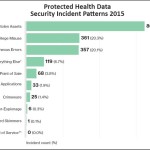
Healthcare is the most-breached business sector, both in the number of breaches and in the number of records compromised, according to research from Gemalto.
But what are the main causes of data breaches in healthcare? What can you do to prevent them and protect your clients? We dig into Verizon’s 2015 Protected Health Information Data Breach Report to tell you.
Continue readingHIPAA is huge and confusing. The regulations are so massive that few people can point to a document and say “this is HIPAA.”
But if you’re an IT service provider, we have narrowed down the parts of HIPAA that matter to you. You can see them in this document. The text in this PDF comes straight from the Code of Federal Regulations, the only official source of the HIPAA guidelines.
Continue reading
Egress filtering is a powerful tool that can disrupt many attacks. It does this by controlling outbound connections from the network and blocking any that are disallowed.
But egress filtering is easy to misconfigure. In this post, you will get a quick review of egress filtering, including tips on where, why, and how to deploy it.
Continue readingHealthcare IT is a fantastic market to break into. Potential clients are high in number and your IT services are in high demand due to regulations like HIPAA and constant news stories about data breaches.
How can you make it easier to sell IT services in healthcare? We interviewed a Calyptix reseller partner who has been rapidly growing in the healthcare industry. Get four simple tips in this article.
Continue reading
The deadline for merchants to accept EMV “chip cards” is here. Anyone who accepts credit card payments now has to use the new chip-card method or risk having to repay the money lost in fraudulent transactions.
Are your clients at risk? Check this post to get up to speed on the EMV card deadline, what it means for your clients, and how this can be a big sales opportunity for your business.
Continue reading
Need a few examples of small businesses hit by cyber attacks? This article has three examples to show how a simple phishing email or malware infection can bring huge losses.
Also: did you know that banks are not required to repay funds stolen from a business account? You’ll see why in this article. Show your clients to make sure they realize: once a hacker has their money, it’s gone.
Continue reading
The last two years have been filled with news reports about major data breaches. First, we heard about millions of records compromised at retailers like Target and Home Depot. Now major healthcare organizations are getting hit.
Why is this happening? In this post, see four top reasons why healthcare networks are a major target for data breaches, and why the criminals seem to be winning the war.
Continue reading
The web is flooded with malware. Most users don’t have a clue on how to avoid it. What if you could give your clients three simple ways to stay safe? Would you save time and money?
See three easy-to-follow rules that will dramatically reduce the chances of a malware infection. They come from Spam Nation, the best-selling book by cyber security journalist Brian Krebs.
Continue reading
Criminals are placing ads on some of the most popular sites on the web. The scariest part: the ads can infect users with malware without even clicking.
Learn more about the rapidly growing threat called “malvertising.” Find out how attackers are combining zero-day exploits, malware, and online ads for a powerful attack strategy, and see how you can avoid it.
Continue reading
Wire fraud is the modern-day bank heist. Instead of masks and guns, thieves use stolen email credentials and clever deception to snatch thousands of dollars. How do these heists begin? With stolen data.
Get a quick overview of wire fraud tactics so you can protect your business and your clients. See how thieves steal the data, fool the banks, and make off with the money.
Continue reading