Do not underestimate the importance of a HIPAA risk assessment.
That’s one insight to emerge from the latest HIPAA penalties announced by the Office of Civil Rights (OCR) this month.
OCR is the federal department responsible for enforcing the healthcare data security regulations known as HIPAA.
In the first week of November, OCR announced two big HIPAA penalties:
What do both cases have in common?
Neither organization performed an adequate risk assessment beforehand, according to press releases from OCR’s parent department, the U.S. Department of Health and Human Services (HHS).
The violations at URMC included the loss of an unencrypted flash drive in 2013 and the theft of an unencrypted laptop in 2017.
An OCR investigation found the organization also failed to:
This resulted in a $3 million “settlement”, i.e. penalty, to be paid by URMC.
This wasn’t URMC’s first tango with OCR. The organization had been investigated in 2010 for the loss of an unencrypted flash drive, according to a HHS press release.
Apparently, that prior investigation, and URMC’s prior acknowledgement that its failure to encrypt ePHI was risky, were not enough to motivate the organization to change course.
 HIPAA Violation: Insecure Web Application
HIPAA Violation: Insecure Web ApplicationThe breach at TX HHSC occurred when one or more employees moved an internal application from a private, secure server to a public one.
The application included a security flaw and the ePHI of more than 6,600 patients. When moved to a public server, the flaw exposed those records to the world.
Due to a lack of audit controls, the organization also had no way of knowing the number of unauthorized parties who accessed the ePHI, according to a HHS press release.
The department responsible for the breach filed a report with OCR in 2015. This triggered an investigation, which revealed the organization also failed to:
OCR imposed a penalty of $1.6 million last month. TX HHSC apparently did not contest the findings and waived its right to a hearing.
Penalties of $3 million and $1.6 million – for a couple lost drives and a software flaw? Well, not exactly.
The negligence of each organization – their failure to conduct risk assessments and enact adequate controls – undoubtedly contributed to the penalties they received.
Risk assessments have been required for covered entities – even small ones – for at least 15 years by HIPAA. They’ve been required for business associates for just over five years.
An argument that you didn’t have the time or resources to conduct a good risk assessment is likely to fall on deaf ears if the OCR is digging through your company after a breach.
If you’re required to comply with HIPAA, then you are required to regularly complete a risk assessment.
Will failure to complete an assessment result in a greater penalty? We cannot say for certain, but it certainly will not help and might even make a breach more likely.
 Free HIPAA Risk Assessment Tool
Free HIPAA Risk Assessment ToolOCR’s website lists seven resolution agreements for 2019 so far. These are civil penalties, settlements, etc. for HIPAA violations.
In five of the seven cases (71%), the breached organization did not conducted an adequate risk assessment (or any) beforehand.
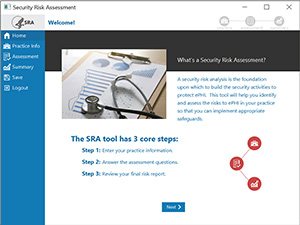
OCR also announced on Oct. 31 an update to its HIPAA Security Risk Assessment Tool.
The tool is designed for small and medium organizations and is free to download (updated version is for Windows only).
It walks users through a series of modules and questions to help evaluate and document potential threats and vulnerabilities to ePHI in their organizations.
A good overview of the tool and its workflow is provided in a slide deck on HealthIT.gov.
In short, users enter lists of important items, such as assets, vendors, and business associates. Items can be entered manually or uploaded via CSV.
A series of questions walk users through the process of identifying threats and vulnerabilities, scoring their likelihood of occurring, and their impact if they occurred.
A summary report provides risk scores, areas for review, and a total number of vulnerabilities identified as applicable to the organization.
The tool is worth a look – especially for smaller healthcare organizations and their IT providers.
Whether you use the tool or not, one way or another, you must complete a security risk assessment to comply with HIPAA.
5 Biggest Data Breaches at HIPAA Business Associates in 2019 (So Far)
HIPAA Compliance for IT Providers: Top 5 questions
HIPAA Security Rules for IT: What are they?
Top 3 causes of HIPAA violations and their simple solutions