A new and dangerous strain of ransomware exploded onto the web last week, seizing an estimated 300,000 computer systems in just a few days.
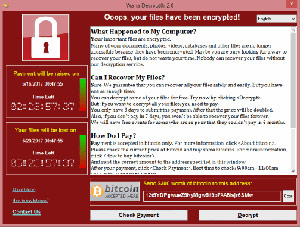
WannaCry ransomware (a.k.a. WannaCrypt, WannaCrypt0r 2.0) knocked out systems at major hospitals, telecoms, schools, governments and other organizations, demanding $300 to $600 in Bitcoin to release each machine infected.
WannaCry reached more than 150 countries in less than five days. A Europol spokesman called it the “biggest ransomware attack ever” according to the Washington Post.
And the threat isn’t over.
We’ve seen crypto-ransomware before. WannaCry follows the same model:
But we’ve never seen ransomware spread like this before.
Ransomware families like Cryptolocker, Locky, and Petya, often spread through malicious emails, drive-by downloads, and other tactics that require the user to take action.
WannaCry doesn’t wait for a user to act. The initial infection on a network may occur via malicious email, but subsequent infections are automatically performed with worm techniques that find and attack new victims.
Once a machine is infected with WannaCry, the malware scans connected the LANs and WANs to find and attack other vulnerable hosts.
This allows WannaCry to seize entire networks and even hop to others. This is how its infection rate shot off like a rocket.
 EternalBlue Exploit in WannaCry
EternalBlue Exploit in WannaCryWannaCry uses the EternalBlue exploit to breach Windows machines. This exploit allegedly came from a cache of cyber weapons stolen from the U.S. National Security Administration (NSA) and released publicly on April 14.
The exploit targets a vulnerability in Windows Server Message Block version 1 (SMBv1), a legacy network file-sharing protocol. Microsoft released a patch for this vulnerability on March 14 (Microsoft Security Bulletin MS17-010).
This vulnerability is present on all Windows machines that have not been updated since before March.
All Windows machines that have not been patched since before March are vulnerable to a WannaCry ransomware infection without any interaction from the user.
Patched Windows systems can be infected by other means, such as clicking on a malicious email link or opening a malicious attachment.
Imagine a usual day at work.
Now imagine all the computer systems are “down” – all electronic files have been seized by a nasty computer virus that demands payment in Bitcoins – and you don’t even know how to obtain Bitcoins.
For you, that day could be tomorrow if you’re not careful.
For the National Health Service (the United Kingdom’s health system) and Telefonica, the largest telcom in Spain, that day was last Friday.
 Didn’t someone stop WannaCry?
Didn’t someone stop WannaCry?Nope.
On Friday May 12, a UK-based cybersecurity researcher threw a wrench into the gears of the WannaCry ransomware machine. He discovered a domain used by the ransomware, possibly as a kill switch or sandboxing avoidance technique.
Originally, when installing, WannaCry attempted to connect to a specific domain (which was a long stream of gibberish characters followed by .com). If the connection failed, the installation continued. If the connection succeeded, the installation halted.
By spending $10.69 to register the domain – the researcher ensured any system attempting to connect to it succeeded, thus halting installations and greatly slowing the ransomware’s spread.
Unfortunately, the malware’s authors have since updated WannaCry’s code and the threat lives on. However, the spread appears to have slowed greatly.
You can also count on other criminals to learn from WannaCry’s innovative approach to online extortion. It is only one example from a vast series of ransomware families that continue to strengthen and evolve.
 What should I do?
What should I do?Patch Windows – The most import step is to ensure all Window systems are patched and up to date. This includes Windows systems on the other side of VPN tunnels.
Isolate Vulnerable Systems – Any Windows systems that cannot be updated should be isolated or removed from the network.
Review Firewall Settings – Check the settings of AccessEnforcer UTM Firewalls, and any other UTM devices, to ensure they do not have configurations that can allow WannaCry to scan and attack their networks.
Specifically, block inbound traffic on TCP ports 139 and 445, because WannaCry uses them to spread. Do not use port forwarding rules or other configurations that might leave these ports open.
Also – check with your firewall vendor for specific instructions on further preventing WannaCry. Calyptix published instructions for AccessEnforcer UTM Firewalls in the Online Portal.
Protect Endpoints – Install an effective anti-malware solution on all machines and keep it updated.
Filter Email – WannaCry may spread via worm techniques, but the initial infection on a network can easily occur through one of ransomware’s favorite tactics: phishing emails. So keep your inboxes clean.
Keep backups – When a computer is infected with ransomware, a good backup can turn a potential disaster into a mere hassle. Maintain backups of your critical files and systems. Test them periodically, and always keep a set offline.
For more tips, check this post: Ransomware Prevention: 5 Ways to Avoid a Crisis.
Microsoft Security Bulletin MS17-010
The worm that spreads WanaCrypt0r
US-Cert: Alert (TA17-132A) - Indicators Associated With WannaCry Ransomware