A data breach will cost money to clean up. The question is, how much? The answer is up to you.
Many factors decide the total cost of a breach, and a surprising number are within your control.
The factors shown to cut cost the most are revealed in research from Ponemon Institute.
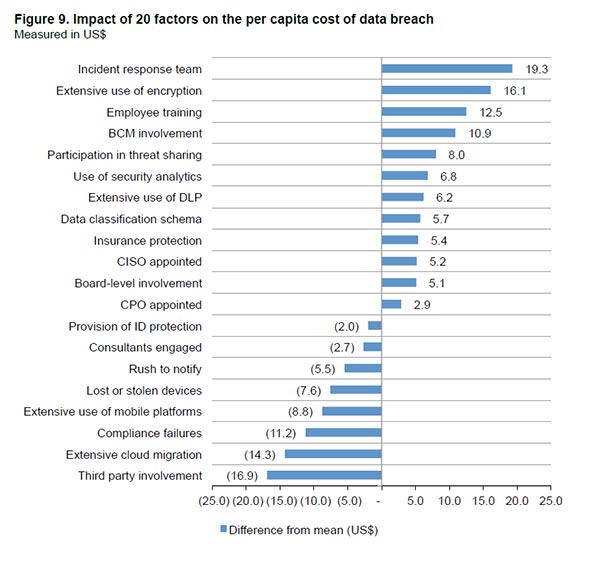
Below, we review the top 10 ways to reduce the cost of data breach, via the Ponemon Institute Cost of Data Breach 2017 study. It’s is based on an analysis of breaches in 419 companies.
When a functioning incident response team is in place, the cost of a data breach is reduced $19 per record on average, according to the Ponemon report.
Who should be on an incident response team? A successful team includes experienced internal personnel from compliance, IT, legal, and information security.
External members should include computer forensic specialists, outside legal counsel, and a crisis management firm.
 #2. Encryption
#2. EncryptionExtensive use of encryption throughout a company reduced the average cost of a data breach by $16 per record.
“Encryption” is a broad term and it’s important to make sure you are protecting both data at rest and data in transit.
Data at rest refers to data in storage, such as files saved on a computer, server, or mobile device. Encrypting this data helps ensure it is unlikely to be accessed if stolen without a means to decrypt it.
Data in transit refers to data as it moves – such as when sending an email, when downloading a webpage, or when applications use data. Similar to data at rest, encrypting this data helps ensure it is unlikely to be useful if stolen without a means to decrypt it.
When employees were trained to recognize methods of cyberattacks, the cost of a data breach decreased by an average $12.5 per record.
Training should include information on effective use and storage of passwords, how to spot and avoid phishing emails, how to responsibly handle sensitive data, and the consequences of a major breach.
 #4. Business Continuity Management (BCM)
#4. Business Continuity Management (BCM)Business continuity management is the practice of identifying the threats to an organization and preparing to quickly recover should any of those threats be realized.
The threat of data breach is growing across the world. The wisest organizations are executing plans to minimize the risks and quickly recover if one strikes – and thereby maintain “continuity.”
The Ponemon Institute found that when a company has BCM in place, the average cost breached record fell by $10.9.
The researchers found that organizations with an active BCM strategy reaped many benefits:
Threat intelligence sharing platforms allow organizations to share information about cyber-threats so they are identified and blocked more efficiently and effectively.
An example is the Cyber Threat Alliance, a platform where cybersecurity experts share contextualized, actionable cyber threat intelligence.
The National Institute of Standards and Technology published a Guide to Cyber Threat Information Sharing. It defines cyber threat information as “indicators of compromise, tactics, techniques and procedures used by threat actors.”
Participation in threat sharing saved an average $8 per breached record.
 #6. Security Analytics Use
#6. Security Analytics UseThe deployment of security analytics resulted in an average savings of $7 per compromised record.
Security analytics is the analysis of data to improve security. Oftentimes, analytics are used to identify emerging threats and stop them before they take root.
The types of data reviewed may include log and event data, network traffic flows, transaction records, and many other types of information about the network, endpoints, and users.
Practicing data loss prevention saved an average $6.2 per compromised record.
DLP has dual meanings.
First, it can describe software products that a network administer uses to manage the information end users can access.
Second, it can also describe the tools and strategies used to prevent end users from sharing sensitive information outside of an organization’s network.
 #8. Data Classification
#8. Data ClassificationData or information classification is crucial to establishing a baseline of what security controls are needed to protect specific data.
Only by classifying their data can organizations then establish and follow security policies that provide adequate controls for each type.
For example, customer credit card data is likely to require a greater level of security than the files on an intern’s computer. However, first the organization must classify the data and identify where it resides – otherwise it cannot be protected.
With data classification in place there was an average $5.7 savings per compromised record.
Data breach insurance policies come in many different packages, and it reduced data breach costs by $5.2 per record on average.
In most U.S. states, cyber security coverage can be used for legal defense and liability expenses if a company is party to a lawsuit.
Liability coverage can also provide network security services, employee training, internal policy and procedure development, and incidence response planning.
The last three factors that decrease the per capita record cost of a data breach are staff-related.
An organization with a Chief Information Security Officer in place saved $5.2 per record.
Savings also result when an organization has board level involvement ($5.1 per record) and a Chief Performance Officer ($2.9 per record).
The more employees with a comprehensive knowledge of corporate security matters, the greater the savings it seems.
CSO Online: Building a Data Breach Response Team Before You Have a Breach
Crypteron: The Real Problem With Encryption
NIST Guide to Cyber Threat Information Sharing
Govtech.com Don't Rush the Security Breach Notification Timeline