 You’ve heard the news and so have your clients. Healthcare organizations are getting hit with data breaches, and the federal government is handing out steep fines for HIPAA violations.
You’ve heard the news and so have your clients. Healthcare organizations are getting hit with data breaches, and the federal government is handing out steep fines for HIPAA violations.
Hopefully your healthcare clients have gotten the message and have fallen in line with HIPAA. But in case they haven’t, here is another thing they should worry about: their reputation.
HIPAA practically requires healthcare organizations to harm their reputations after a data breach. The breach notification rules amount to an anti-marketing campaign, costing the organization time and money to throw mud onto its brand. Ouch.
Make sure your healthcare clients understand that if they have a data breach, word will get out. In fact, it’s practically required.
Here are a few ways that a hacked healthcare organization has to market against itself with breach notifications:
Related: HIPAA for IT Providers: The most important rules to know
The homepage is typically the most popular page of a website. It’s prime real estate online, and anything posted there receives ample attention.
If a healthcare organization does not have accurate contact information for more than 10 people affected by a data breach, then HIPAA compliance requires “conspicuous posting” of a breach notification on its homepage for 90 days.
In addition, the organization has to include a toll-free number that remains active for 90 days that people can call to learn if the breach affects their health data.
Here’s an example from UCLA Health’s homepage in response to a recent data breach:
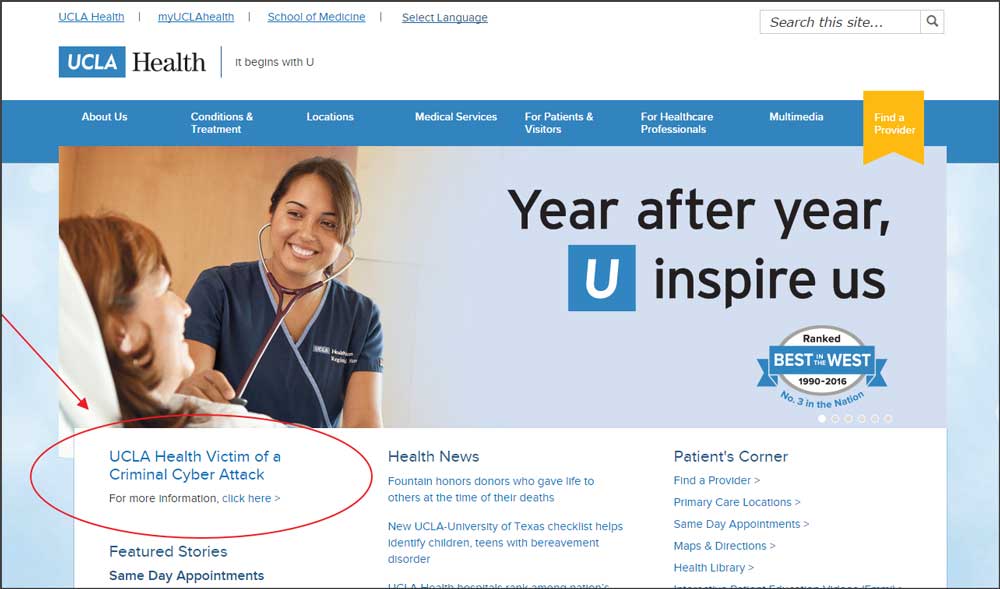
The link circled above points to UCLA Health’s notice with more detail on the breach.
Advertise in the press
As an alternative, the organization can run a “conspicuous notice” in a major print or broadcast media outlet in the region. Imagine paying thousands of dollars for an advertisement that pushes people away from your business.
The organization may have to start a negative PR effort. For breaches affecting more than 500 people, the organization has to contact prominent media outlets in the region and notify them of the breach within 60 days.
The media are likely to run news stories about the breach. That’s why stories, such as the one this week about a data breach at UCLA’s health system affecting 4.5 million people, never seem to stop coming.
Let’s not forget the anti-marketing by direct mail. Healthcare organizations have to notify every person whose health data was disclosed in a breach. If a person is deceased, then the next of kin has to be notified.
The notice must be in writing and sent by first-class mail. Email can be used as an alternative if the person agrees.
Here are two examples:
Related: HIPAA for IT Providers: The most important rules to know
The fun doesn’t stop there. A breached organization has to notify the federal department that enforces HIPAA, the U.S. Department of Health and Human Services. The notice can be sent by submitting a report to the HSS website.
Then the HHS can decide to post about the organization’s breach on its website (and it’s safe to assume the site receives thousands of visitors each month).
This report must be made within 60 days of discovery if more than 500 people are affected. If fewer than 500 were affected, then the report must be made within 60 days of the end of the calendar year.
Financial penalties under HIPAA only a portion of the total cost of a breach. Additional legal fees, consultant fees, and the cost of resolving security vulnerabilities also pile on.
The damage to reputation and brand should not be understated – especially since HIPAA forces breached organizations to spend thousands of dollars marketing against themselves with notifications spread far and wide. Warn your clients.
HIPAA Security Rules for IT: What are they?
HIPAA Security: Most business associates suffer data breaches