 HIPAA tries to force healthcare organizations to protect patient data – but does it work?
HIPAA tries to force healthcare organizations to protect patient data – but does it work?
Any health IT professional will tell you, HIPAA compliance alone does not guarantee security. HIPAA is not a complete security framework and it’s not enough to protect ePHI.
Many hospitals, doctor’s offices, and others – while striving for HIPAA compliance – also follow one or more security frameworks that have earned widespread respect and adoption in the infosec industry.
A cyber security framework is a proven approach to developing the policies and procedures necessary to secure the confidentiality, integrity, and availability of information systems and data.
In short: they roadmaps for securing IT systems.
Healthcare organizations can select from a number of frameworks that are widely respected and regularly maintained.
This table shows the most popular cyber security frameworks in healthcare, according to the 2018 HIMSS Cybersecurity Survey.
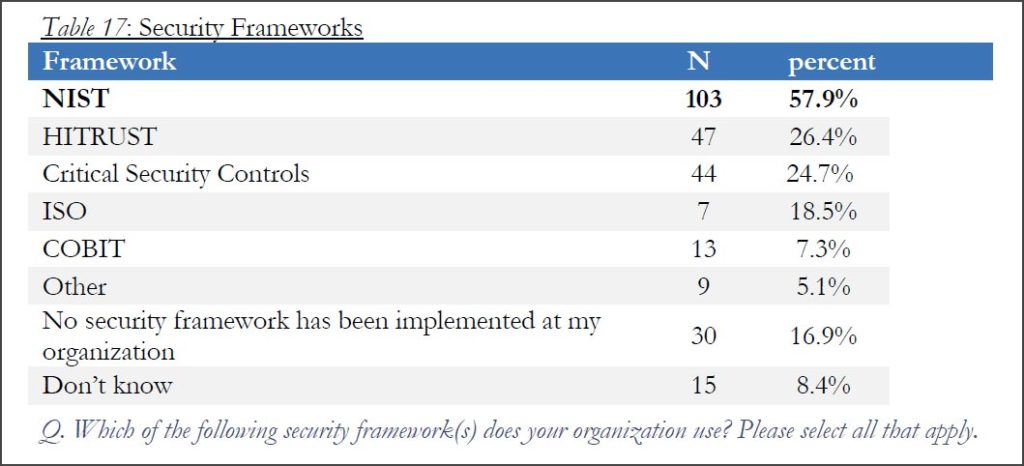
HIMSS surveyed 239 healthcare information security professionals from Dec. 2017 through Jan. 2018 for the report. When asked to list the network security frameworks used at their organizations, respondents could select multiple answers.
Below, we highlight the most popular frameworks listed and note a few that didn’t make the cut.
 Framework #1. NIST
Framework #1. NISTThe most popular security framework in healthcare is listed as “NIST”, with 57.9% of respondents reporting its use at their organizations.
NIST is the National Institute of Standards and Technology, the U.S. agency that develops many technical standards and guidelines, including for information security. It’s one of the many agencies under the U.S. Department of Commerce.
NIST maintains several documents that are widely considered gold standards for network and data security. While they are typically intended for U.S. federal agencies, they are also widely used in the private sector.
Here are three of the most popular:
This document is intended to help improve cyber security risk management in critical infrastructure in the U.S.
This document is a catalog of security and privacy controls that must be followed by federal agencies. It applies to all federal information systems other than those systems designated as national security systems.
The document is used by federal agencies in contracts and other agreements. In general, it sets data security standards that must be followed by organizations that do business with the federal government.
In previous posts, we’ve recommended NIST SP 800-171 as a solid security framework for small businesses.
 Framework #2. HITRUST
Framework #2. HITRUSTSlightly more than one-quarter of respondents (26.4%) say their organization followed the security framework maintained by the Health Information Trust Alliance (HITRUST).
HITRUST Alliance is a private organization led by representatives from some of the biggest names in healthcare, including Anthem, Humana, UnitedHealth, and Walgreens.
The organization maintains the Common Security Framework (CSF), a set of guidelines for information security designed specifically for the healthcare sector.
HITRUST CSF v9.1 is the latest version of the framework, published in Feb. 2018.
 Framework #3. CIS Critical Security Controls
Framework #3. CIS Critical Security ControlsSlightly less than one-half (24.7%) of respondents said they are following the Critical Security Controls.
Center for Internet Security (CIS) is a nonprofit organization that maintains the 20 Critical Security Controls (CSC, formerly known as the SANS 20). The CSC is a list of cyber security practices intended to stop the most common attacks.
The controls are listed in order of priority – starting with the most important – such as creating an inventory of assets, managing vulnerabilities, and controlling the use of administrative privileges.
While implementing the controls can be of immense value, they are not intended to provide a complete cyber security framework. Instead, the CIS 20 are often used alongside other frameworks, such as NIST’s.
Version 7 of the CIS 20 Controls was released in March 2018.

ISO refers to the International Organization for Standardization, a non-governmen tal organization that publishes standards to facilitate world trade. Membership is comprised by representatives from standardization agencies in more than 160 countries.
Along with the International Electrotechnical Commission (IEC), ISO maintains a series of standards for creating and maintaining an information security management system, known as ISO/IEC 27000 – or simply “the ISO”.
Among respondents, 18.5% use the ISO framework.
There are actually dozens of related standards (ISO/IEC 27001, 27002, 27003, etc.) – however, the requirements for information security are listed under 27001. Others listed under 27000 are “codes of practice” or definitions to be used to in support of the requirements in 27001.
ISO/IEC 27001 Information Security Management Systems Requirements is the latest version, published in 2013.
 Framework #5. COBIT
Framework #5. COBITCOBIT refers Control Objectives for Information and Related Technologies, a security framework created by ISACA (formerly known as “Information Systems Audit and Control Association” but which today is known by the acronym only).
About 7.3% of respondents follow COBIT.
ISACA is a nonprofit organization that creates and maintains sets of standards and practices for information systems. The group describes its COBIT 5 framework as the “overarching business and management framework for governance and management of enterprise IT.”
COBIT 5, the latest version of the framework, was released in April 2012.
Shelter from Cyber Regulation: NIST 800-171
5 Security Controls that Stop 85% of Cyber Attacks
Network Inventory Made Easy: 5 Simple Steps