
Remote access software is widely used by small businesses for work-from-home. Yet there are security problems. Adding layers can help shore up protections.
In 2020, the number of people working remotely jumped dramatically. Yet unsafe work-from-home solutions increase the small business’s attack surface. Adding layers of online protection can help you avoid the risk of exposure to cybercriminals.
Remote access software can be invaluable for small businesses. Employees can collaborate securely with file sharing, screen shares, remote meeting and more. This improves productivity for telecommuters and keeps business relationships intact in these turbulent times where we can’t meet face-to-face (or even mask-to-mask).
However, cybercriminals are renowned for taking advantage of current events. You can bet they have stepped up their attacks on remote access software knowing that its use is more widespread globally.
Many organizations have turned to Microsoft’s Remote Desktop Protocol (RDP) to provide reliable, cheap and quick remote access. The RDP feature allows users to access their Windows environment from nearly any kind of device over the network without direct access to the physical machine at the office.
In March 2020 alone there was a 40% increase in the number of computers exposing RDP directly to the Internet, according to Shodan, an internet scanning project. With so many organizations moving to remote work, the increase isn’t that surprising. Yet the reliance on RDP absent safeguards is alarming, especially given the surge in critical vulnerabilities, constant attacks, and public advisories from the FBI and NSA.
Just in the last year, RDP suffered multiple high-profile critical vulnerabilities that can all be exploited by an unauthenticated attacker with no user interaction:
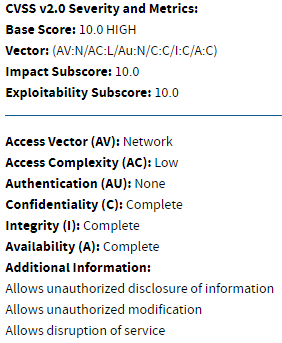
To truly appreciate the severity of these vulnerabilities, consider this: they all were rated 10.0 (out of 10) by NIST for the National Vulnerability Database (NVD). To fully understand the very real nature of this threat to small businesses using RDP, play around with the CVSS scoring calculator. In short, these easy to implement vulnerabilities have really high impact potential, which makes them really nasty for small businesses.
RDP is the favorite target for attackers, by a landslide, Calyptix’s internal research reveals as much as 89% of all inbound network attacks target RDP. Incident response researchers have also found RDP is the leading vector for ransomware infections among small businesses with fewer than 100 employees. To make matters worse, because RDP attacks don’t require user input, they are difficult to detect, contributing to increasing ransoms paid by victims.
For small businesses using RDP and other remote access tools without adequate safeguards, it’s only a matter of time before they will be compromised. Persistent poor configurations, weak passwords, and critical public facing vulnerabilities all have attackers salivating as they continue to pursue these vulnerable targets.
So, what can the small business do to secure its remote desktop connections? We’ll discuss that next.
Securing Your Remote Desktop Connections
Small businesses and their IT administrators typically can’t control RDP design. Yet, there are still ways to lessen a company’s exposure to attack.
 You could, of course, educate employees (again, presumably) about the dangers of weak passwords. Passwords are the first line of defense, yet people continue to leave default passwords unchanged or rely on the patently obvious “password” or “12345678.”
You could, of course, educate employees (again, presumably) about the dangers of weak passwords. Passwords are the first line of defense, yet people continue to leave default passwords unchanged or rely on the patently obvious “password” or “12345678.”
The FBI also recommends a network audit to identify systems using RDP, installing available patches, and disabling “the service if unneeded.” Yet doing without remote access software is not practical for many businesses who need RDP enabled for emergency use.
Limiting administrator access to the remote desktop is also smart. In the same vein as only offering access privileges to those who require that software or system, you should consider removing any excess users from the remote desktop user group.
Another strategy is to enable lockout policies to prevent hackers from manually or using automated brute force attacks to guess passwords. You could also make two-factor authentication (2FA) mandatory or move away from passwords to another form of authentication. Despite the vast array of content, guidance and other resources readily available to prescribe how to implement security best practices for RDP, many small (and even large) businesses continue struggle with safeguarding RDP. Let’s consider the added layers of protection Calyptix offers as part of its new AccessEnforcer release.
Calyptix Protects Your Public Internet Exposure
Calyptix’s Gatekeeper, a feature of AccessEnforcer v5.0 and later, provides authenticated remote access without having to expose the RDP port to the public Internet. In addition, it also protects SSH hosts in the same way. End users are required to authenticate themselves via both Active Directory credentials and a 2FA verification code before they can access the RDP or SSH host.
The secure and convenient Gatekeeper feature works with multiple mobile devices to offer:
In addition to Gatekeeper, AccessEnforcer 5.0 also introduces Geo-Fence which adds another layer of protection. With Geo-Fence you can allow or block inbound traffic based on the designated country of origin for the source IP address. If the IP source country is unassigned you can also set up a policy to either allow or block that traffic.

Calyptix recently introduced Geo Fence to meet the need to harden IT environments. The virtual fence around the business network dictates what users can get in, based on where they are trying to gain access from. For instance, if bad actors in North Korea bought user credentials on the Dark Web, access would still be blocked because they were trying to connect from a physical location that is not approved.
Geo Fence instantly eliminates attack vectors malicious cyber actors use to target your network by as much as 80%.
You can specify your Geo Fence Policy by selecting countries to allow or block using the world map, a country table, or the continent table. Plus, if you want to block Russia, but you have a few vendors there, you can whitelist those IP addresses to continue to allow their inbound traffic. Geo-Fence also automatically ensures you don’t inadvertently block your resident country!
Together with Gatekeeper secure network authentication, the Geo-Fence policy helps keep small businesses that rely on remote access software a step ahead of the cyber bad guys. Combining geofencing and MFA won’t make you invulnerable, but the added layers of security will make your business that much more difficult to infiltrate.
Calyptix Security’s AccessEnforcer 5.0 is an ideal work from home solution for small businesses. Learn more about the software and our newest feature innovations today.