IT security trends come and go but one thing remains constant: a steady improvement in the tactics of malicious threats.
Mandiant’s latest threat report gives us a snapshot of how these threats advanced last year. The data is pulled from the experience of the company’s consultants in their role as first responders to critical security events.
Key insights from the report:
Phishing is a simple tactic that continues to bring results for attackers, and they apparently have the most success when posing as the resident IT expert.
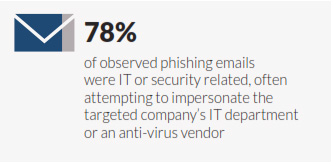
Three out of four (78%) phishing emails observed by the team impersonated the company’s IT staff or an antivirus solution.
Mandiant also saw more targeted spear-phishing techniques used last year to target financial organizations both for initial infection and to regain access after remediation.
EMV cards, also known as “chip and pin” or “chip and signature” cards, will soon be standard in the US. Merchants must accept them by October 2015 or become liable for all card-present fraud on their systems.
In countries that have adopted EMV technology, Mandiant’s team has seen an increase in compromises at ecommerce companies and payment processors.
This echoes a security trend in Canada that we highlighted in a previous post PCI compliance. Canada adopted EMV cards in 2008 and has seen a steady decline in counterfeit-based fraud.
This chart is from the Verizon 2015 PCI Compliance Report:
However, card-not-present fraud continues to climb in Canada and has eclipsed the counterfeit fraud seen previously. This is likely due to criminals changing tactics in response to improved card security.
Most victims are notified of a breach by an outside source, such as a law enforcement agency or business partner. One network security trend is a steady rise in this number.
In 2014, 69% were notified by an outside source. That’s up from 67% in 2013 and 63% in 2012.
While the cause of the trend is difficult to pin down, the number of organizations caught unaware is clearly too high.
This lack of awareness contributes to the long exposure times experienced by most victims. The median number of days a threat was present on a network before discovery in 2014 was 205 days, or longer than six months, according to Mandiant’s report.
The longest presence the team uncovered lasted 2,982 days -- over eight years!
While this security trend is heading in the right direction (the median number of days before discovery is 24 days lower than last year) it’s still too high. Ignorance may be bliss to some, but in this case it’s pain.
In 2014, the team saw more cases in which attackers gained access to the victim’s VPN system than ever before. Two common techniques:
The authors also see a trend in which attackers are able to access certificates that were distributed insecurely, such as in email attachments or open network shares.
When the SSL bug known as Heartbleed went public in April last year, some researchers questioned whether the vulnerability could enable a real attack or if it was only a network security threat in theory.
It did not take long to confirm the threat was real. Within several weeks, Mandiant witnessed attacks that leveraged Heartbleed. One attacker used it against a VPN device to hijack authenticated sessions and gain access without credentials, according to the report.
Two of the three most-attacked industries in 2014 are not surprising. They are retail and financial services, two areas where large amounts of money changes hands, and crooks are attracted to money like rats to cheese.
A surprising trend in Mandiant’s report is the growth in attacks on business and professional services. Coming in at the top spot, this industry’s report attacks grew sharply to 17% of all incidents investigated in 2014 compared to only 4% a year prior. That’s more than a 300% increase.
Two other industries that grew into sizeable targets are government/NGOs and healthcare organizations.
Although anecdotal, the Mandiant report shares interesting examples of advanced social engineering.
One attacker, a suspected nation-state, created a fake female persona to probe employees at a target company. The persona contacted one employee on a popular social network, and after three weeks of messaging she sent a “resume” to the employee’s personal email address.
The resume was actually a backdoor. The attacker also probed other employees, asking the name of their IT manager and what versions of software they used.
DDoS Attacks: Trends show a stronger threat in 2015
HIPAA 2015: Expect more attacks, enforcement, and lawsuits
4 Security Insights via 2014 Verizon Data Breach Investigations Report