Email phishing may not be the newest hacker scam on the market, but it’s certainly one of the most popular. After all, 85% of organizations have reported falling victim to a phishing attack.
If that isn’t enough to convince you that email phishing is a serious problem, let us remind you that 30% of phishing emails are opened by their intended targets, according to the 2016 Verizon Data Breach Investigations Report.
Dialogue within the IT community has been circling the topic of email phishing along with similar attacks for a while, and it appears professionals across the board agree – the best way to combat these attacks and those like them is to warn vulnerable employees through network security training.
Half of tackling the problem is understanding it, so we’ve crafted this email phishing infographic just for small IT businesses who need a quick point of reference when briefing clients on email phishing.
This graphic comes from the new special report, Email Phishing for IT Providers, which you can download here for free.
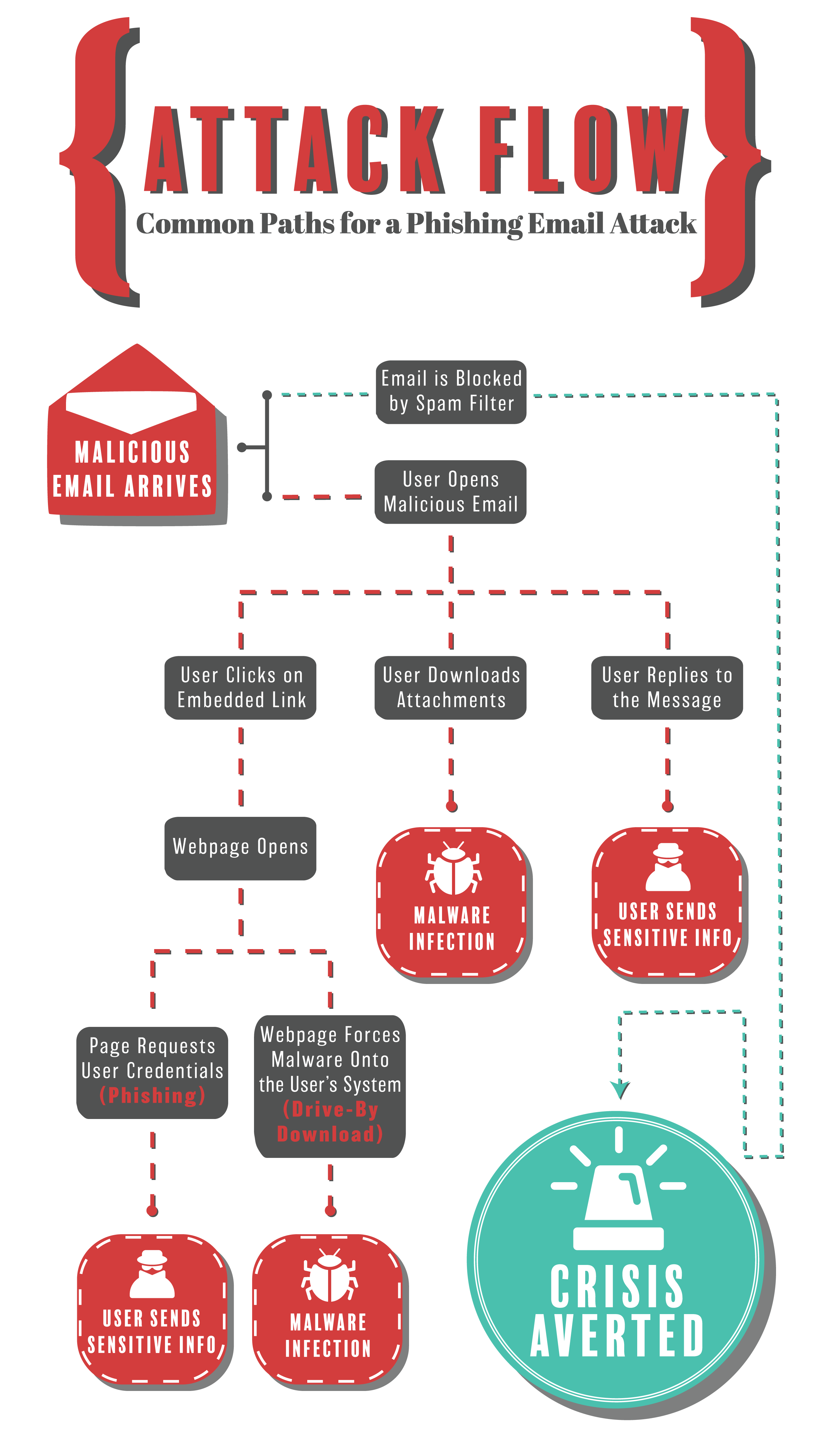
All phishing emails start the same way: a malicious email is sent to a potential victim in hopes of scoring some juicy information, be it credentials or network access.
Even this early on, IT providers have options available to minimize the risk of a successful email phishing attack by installing a spam filter on their client’s network.
Blocking the email before it even reaches its intended recipient is a great way to stop an attack before it starts.
If there is no spam filter in place, the email will likely be delivered. This is where user training becomes essential. Users should know how to spot malicious emails. Otherwise there is a good chance they will open the message and the attack will proceed.
Once a user opens a phishing email, the attack typically proceeds in one of three ways.
Embedded Link
The first route is for the user to click a link in the email that loads an unsafe website.
From there, the webpage will likely open one of the following:
Malicious Attachments
Hackers can also coax users into downloading a malicious attachment. The result can be a nasty malware infection served with a fresh side of major data loss.
Some of the most common types of malicious attachments appear as .doc or .zip files. The message may claim the attachment has important business information such as an invoice or personal material such as photos.
Direct Response
Hackers can and have gotten sensitive information by simply posing as a trusted contact of the victim. Fooled, the victim responds with sensitive information by replying to the email, or even sometimes calling a phone number provided in the attack message.
People, including your clients and employees, can be a little too trusting, which can unfortunately lead to big security problems for your company.
At the end of the day, your company’s network security is in the hands of your least security-savvy employee, which is why on-going training is essential.
Briefing your employees on how to sniff out phishy emails is an easy way to prevent a devastating data breach as well as a great start to implementing a comprehensive network security training program within your company.
5 easy ways small IT departments can train employees on network security
Phishing Attacks: 30% will open a scam email
How to recognize phishing email messages, links, or phone calls