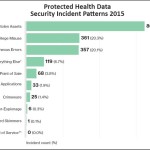
Healthcare is the most-breached business sector, both in the number of breaches and in the number of records compromised, according to research from Gemalto.
But what are the main causes of data breaches in healthcare? What can you do to prevent them and protect your clients? We dig into Verizon’s 2015 Protected Health Information Data Breach Report to tell you.
Continue reading
CryptoWall is the latest strain of ransomware to lock files and demand ransom payments to release them. But does paying the ransom work?
You'll find out inside. You'll also learn more about the threat and how to prevent it from hurting your organization.
Continue reading
Basic wireless router security is terrible and it may be getting worse. We review the results of a hacker contest that found 15 zero-day vulnerabilities in popular SOHO routers.
See which router models are affected, and find out why most of these vulnerabilities have risen from the grave.
Continue reading
Is Cryptolocker really dead? Some researchers have doubts -- even as new types of ransomware continue to attack computers across the globe.
In this post, you'll get an update on Cryptolocker and say "hi" to a new, potentially stronger brand of ransomware: Critroni.
Continue reading Heartbleed is a major security flaw discovered in certain versions of OpenSSL. The bug can allow attackers to eavesdrop on communications, impersonate users, or steal data thought to be encrypted and secure.
Continue reading
Heartbleed is a major security flaw discovered in certain versions of OpenSSL. The bug can allow attackers to eavesdrop on communications, impersonate users, or steal data thought to be encrypted and secure.
Continue reading  DDoS attacks are nothing new, but the storms of traffic they use to drown targets in 2014 have grown into hurricanes.
Continue reading
DDoS attacks are nothing new, but the storms of traffic they use to drown targets in 2014 have grown into hurricanes.
Continue reading