Small office and home office routers (SOHO) can have so many security flaws that a hacker contest has been started to highlight the issue. The contest awards prizes to hackers who can discover new vulnerabilities in 10 popular routers.
What a great time to cover router security! In this post, you get 12 ways to improve the security of your wireless router, and you'll see why it might be best to leave the "routing" of network traffic to another device.
Continue reading
Is Cryptolocker really dead? Some researchers have doubts -- even as new types of ransomware continue to attack computers across the globe.
In this post, you'll get an update on Cryptolocker and say "hi" to a new, potentially stronger brand of ransomware: Critroni.
Continue reading
The war against malware and malicious websites never ends. But with a little intel and some firepower, your team can keep your office and your clients safe.
See the top 10 ISPs that host the most malware. Also find out which countries are rising in the malware market and which file types to watch out for.
Continue reading
Pretend PCI DSS compliance is a highbar. How you handle cardholder data will determine whether you have to throw a small, light portion of your network over the bar or the whole hulking mass of it.
IT service providers can make compliance easier -- but how?
Continue reading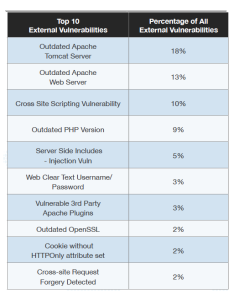
The top cause of security vulnerabilities are outdated and unpatched systems. See the data to prove it, and know which types of systems are more commonly out of date.
Inside you'll see the top 10 external security vulnerabilities, the top 10 internal vulnerabilities, and the most common causes, all found in the 2014 Global Threat Intelligence Report.
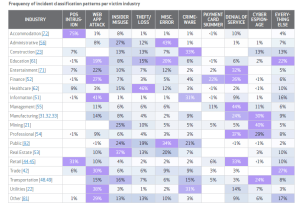
Continue readingThis year's Verizon Data Breach Investigations Report has a lighter tone, but its data and analysis are as sobering as ever.
Get insights and charts from the report, and see which types of security incidents happen most often in your clients' industries.
Continue reading
IT providers, do you have clients in healthcare? Do you handle their patient data? If yes, then you are almost certainly required to protect that data by HIPAA.
HIPAA calls this data “electronic protected health information,” or ePHI. Essentially, it is electronic information about a patient. It can be anything from a patient’s phone number to a recent diagnosis.
HIPAA requires healthcare organizations to protect this data. It also requires their “business associates” to protect it – and that includes their IT service providers.
Continue reading